Delving into the technical specifications of a security appliance is crucial for understanding its capabilities. The Checkpoint 6600 Datasheet is a key document that provides all the vital information about this powerful security platform. Whether you're a network administrator, a security professional, or an IT decision-maker, this datasheet serves as your definitive guide to the Checkpoint 6600's features, performance, and deployment options.
What Is The Checkpoint 6600 Datasheet And How Is It Used?
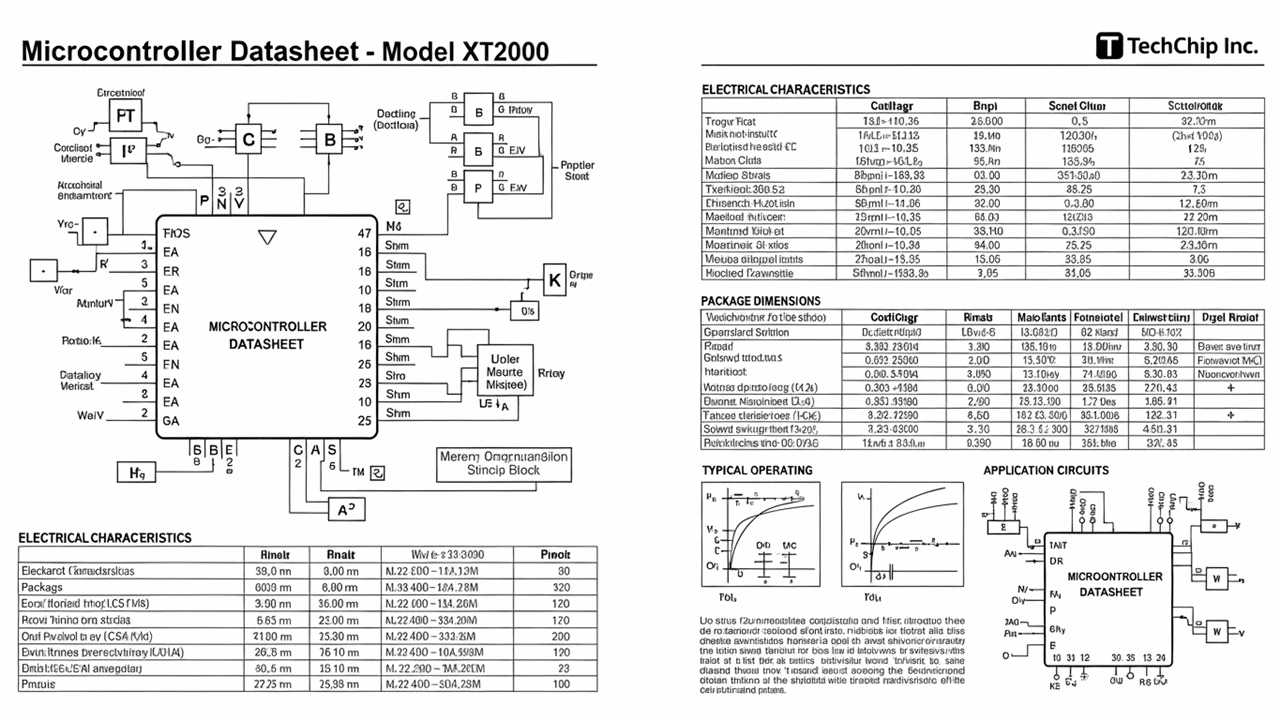
The Checkpoint 6600 Datasheet is a comprehensive technical document that details the hardware specifications, performance metrics, supported features, and connectivity options of the Checkpoint 6600 security gateway. It acts as a blueprint, providing essential data for understanding the device's capabilities in protecting networks from a wide range of cyber threats. This includes information on processing power, memory, storage, network interfaces, and the various security services it can run, such as firewalling, intrusion prevention, and VPN connectivity. Understanding this datasheet is paramount for ensuring the appliance is correctly sized and configured for your specific security needs.
These datasheets are indispensable tools for several key purposes. IT professionals use them to:
- Evaluate if the Checkpoint 6600 meets the performance requirements for their network traffic.
- Determine the types of security policies and services that can be implemented.
- Plan for integration into existing network infrastructure.
- Compare the 6600 against other security solutions.
The information within the Checkpoint 6600 Datasheet is typically presented in a structured format, often including tables that clearly outline technical parameters. For example, you might find a table like this:
| Feature | Specification |
|---|---|
| Firewall Throughput | Up to 30 Gbps |
| VPN Throughput | Up to 10 Gbps |
| Connections Per Second | Up to 250,000 |
This level of detail allows for informed decision-making. Furthermore, numbered lists within the datasheet might detail specific software versions supported or the range of threat prevention features available, such as:
- Advanced Firewall Policies
- Intrusion Prevention System (IPS)
- Threat Emulation
- Anti-Bot and Anti-Virus
To truly grasp the power and applicability of the Checkpoint 6600 for your organization's security posture, you should thoroughly examine the official Checkpoint 6600 Datasheet. This document is your direct gateway to its technical prowess.